Effective governance requires a comprehensive Management Letter on Information Technology General Controls and Cybersecurity to identify system vulnerabilities and operational risks. This report evaluates security protocols, data integrity, and regulatory compliance to strengthen your digital infrastructure against emerging threats. Ensuring robust oversight protects organizational assets and builds stakeholder trust. To assist your documentation process, below are some ready to use template.
Letter Samples List
- Management Letter on Information Technology General Controls Deficiencies
- Cybersecurity Risk Assessment and Mitigation Management Letter
- Information Technology Access and Authentication Controls Letter
- Management Letter on Data Privacy and Cybersecurity Compliance
- Information Technology Change Management and Security Audit Letter
- Cybersecurity Incident Response Preparedness Management Letter
- Management Letter Regarding Cloud Environment Security Controls
- Network Security and Vulnerability Assessment Findings Letter
- Management Letter on User Access Provisioning and Deprovisioning
- Information Technology Disaster Recovery and Continuity Management Letter
- Cybersecurity Threat Vulnerability and Remediation Letter
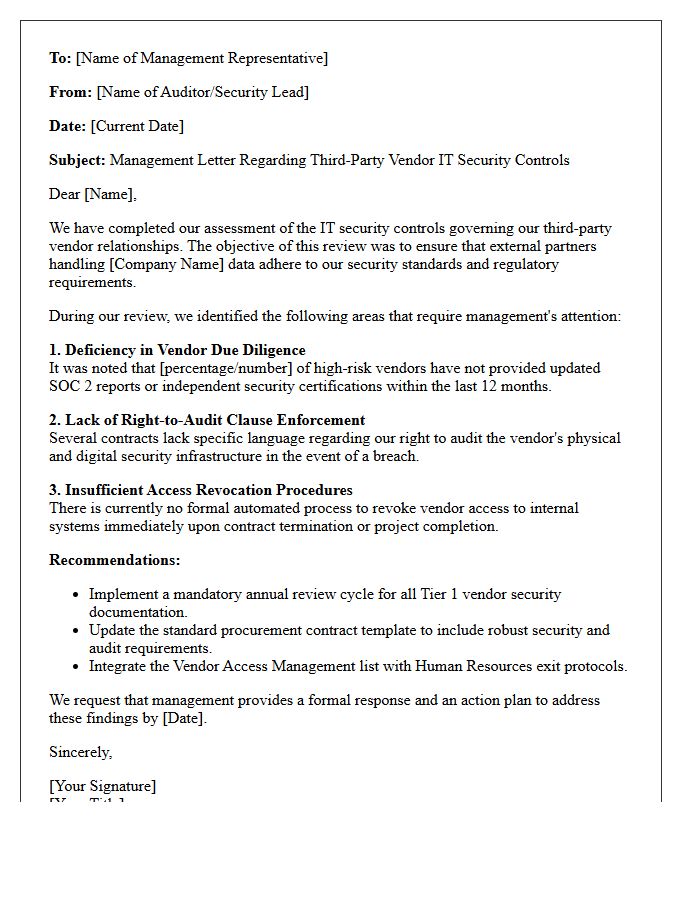
- Management Letter on Third-Party Vendor IT Security Controls
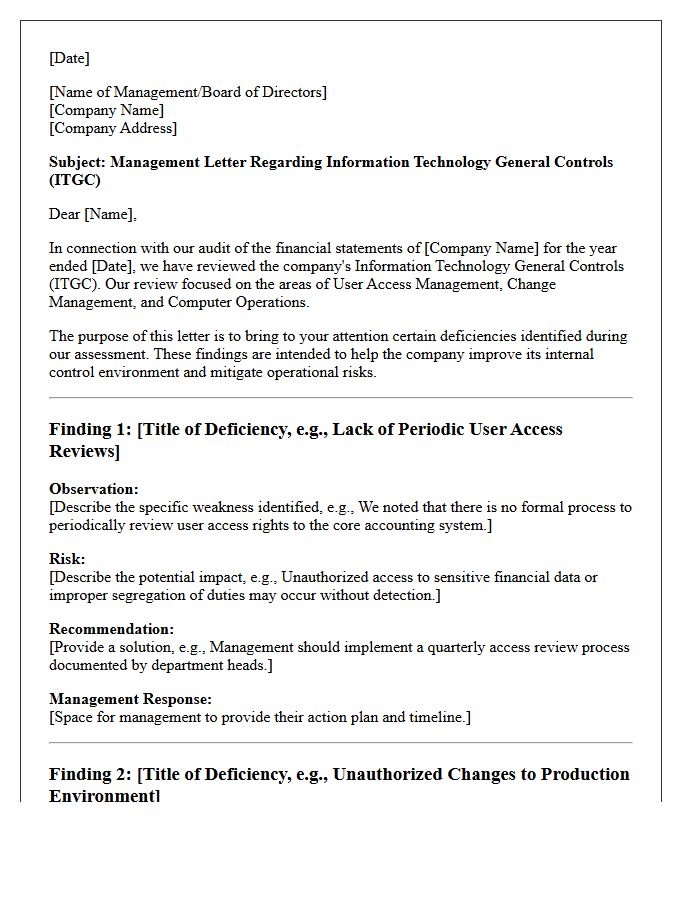
Management Letter on Information Technology General Controls Deficiencies
A Management Letter communicates significant IT General Controls (ITGC) deficiencies identified during an audit. It alerts leadership to security gaps, unauthorized access risks, or system vulnerabilities that could impact financial data integrity. By highlighting material weaknesses and control failures, this document provides actionable recommendations for remediation. Addressing these findings is essential for ensuring regulatory compliance, protecting digital assets, and strengthening the overall IT governance framework to prevent future operational disruptions or data breaches.
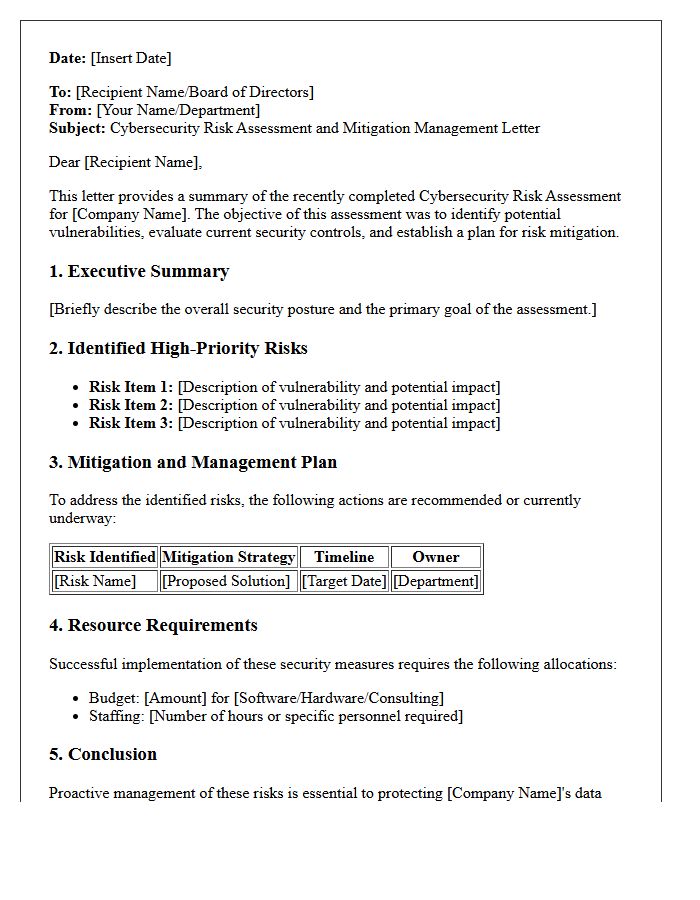
Cybersecurity Risk Assessment and Mitigation Management Letter
A Cybersecurity Risk Assessment and Mitigation Management Letter is a formal document summarizing an organization's digital vulnerabilities. It identifies critical threats to data integrity and outlines specific remediation strategies to minimize exposure. This letter serves as a strategic roadmap for stakeholders, prioritizing security investments based on risk severity. By documenting current gaps and proposed safeguards, it ensures regulatory compliance and strengthens overall resilience against cyberattacks, transforming technical findings into actionable business insights for informed executive decision-making.
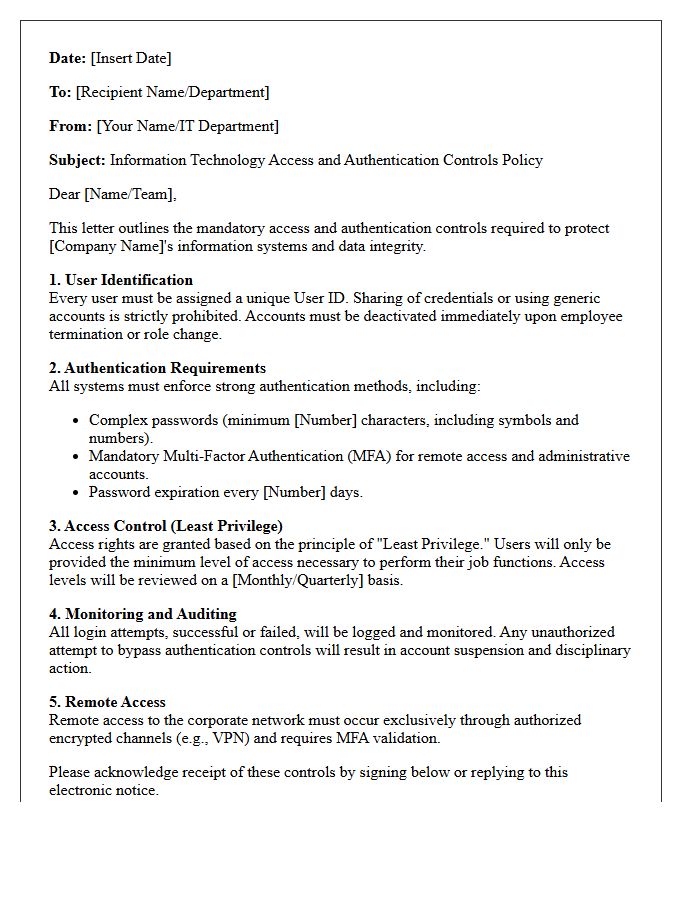
Information Technology Access and Authentication Controls Letter
An Information Technology Access and Authentication Controls Letter is a formal document verifying that an organization maintains robust security protocols to protect sensitive data. It outlines specific identity management practices, such as multi-factor authentication, password policies, and user permission levels. This letter serves as critical evidence during audits or vendor assessments to prove that only authorized personnel can access internal systems. By certifying these logical access controls, businesses demonstrate compliance with industry standards and a commitment to preventing unauthorized data breaches and cyber threats.
Management Letter on Data Privacy and Cybersecurity Compliance
A Management Letter serves as a critical communication tool from auditors to stakeholders, outlining significant gaps in Data Privacy and Cybersecurity Compliance. It identifies internal control weaknesses, such as unauthorized access risks or inadequate data handling procedures. The primary goal is to provide actionable recommendations to mitigate legal liabilities and prevent costly data breaches. By addressing these findings, organizations can strengthen their security posture, ensure regulatory adherence, and protect sensitive information from evolving digital threats, ultimately fostering long-term operational resilience and consumer trust.
Information Technology Change Management and Security Audit Letter
Effective Information Technology Change Management ensures that modifications to IT systems are documented, tested, and authorized to minimize operational risks. A Security Audit Letter serves as formal verification that these control processes meet specific regulatory standards and security benchmarks. This document provides stakeholders with assurance that the organization maintains integrity and availability while preventing unauthorized changes. Proper alignment between change protocols and audit requirements is essential for maintaining a robust compliance posture and protecting sensitive data from vulnerabilities introduced during system updates.
Cybersecurity Incident Response Preparedness Management Letter
A Cybersecurity Incident Response Preparedness Management Letter is a strategic document formalizing an organization's readiness to handle digital threats. It outlines the governance framework, resource allocation, and defined protocols for mitigating breaches. This letter serves as a commitment from leadership to maintain robust incident response capabilities while ensuring regulatory compliance. By documenting roles and recovery objectives, it minimizes operational downtime and protects reputational integrity during a crisis. Ultimately, it validates that the entity is prepared to detect, contain, and eradicate cyber incidents efficiently through structured management oversight.
Management Letter Regarding Cloud Environment Security Controls
A management letter regarding cloud environment security controls evaluates the effectiveness of a service provider's internal controls. It identifies critical vulnerabilities in data protection, access management, and compliance frameworks. This document highlights security gaps that could lead to unauthorized access or data breaches. Understanding these findings is essential for risk mitigation and ensuring that cloud infrastructure aligns with regulatory standards. Organizations must address these recommendations to strengthen their overall security posture and maintain stakeholder trust through robust, audited governance processes in the cloud.
Network Security and Vulnerability Assessment Findings Letter
A Network Security and Vulnerability Assessment Findings Letter is a formal document summarizing security weaknesses identified during a system audit. It provides stakeholders with a high-level overview of critical risks, potential exploit vectors, and recommended remediation steps. This professional communication serves as an essential tool for compliance documentation and risk management, ensuring that technical vulnerabilities are prioritized and addressed. By translating complex scan data into actionable insights, the letter helps organizations strengthen their defensive posture and protect sensitive information from unauthorized access or cyber threats.
Management Letter on User Access Provisioning and Deprovisioning
A management letter on User Access Provisioning and Deprovisioning evaluates the internal controls governing the employee lifecycle. It identifies risks associated with unauthorized access or delayed terminations. Effective provisioning ensures users receive only necessary permissions, while timely deprovisioning prevents security breaches from orphaned accounts. Auditors use this document to recommend automated workflows and periodic access reviews. Implementing these improvements strengthens the organization's cybersecurity posture, ensures regulatory compliance, and mitigates the threat of insider attacks or data exfiltration throughout the workforce transition process.
Information Technology Disaster Recovery and Continuity Management Letter
An Information Technology Disaster Recovery and Continuity Management Letter is a formal document verifying an organization's ability to maintain operations during a crisis. It confirms that resilience strategies are in place to protect critical data and restore systems after a failure. This letter often serves as compliance evidence for stakeholders, auditors, or clients, demonstrating that the business has tested its recovery procedures. By addressing potential risks and downtime mitigation, it ensures operational continuity and builds trust in the organization's commitment to robust security and reliable service delivery under adverse conditions.
Cybersecurity Threat Vulnerability and Remediation Letter
A Cybersecurity Threat Vulnerability and Remediation Letter is a formal notification informing stakeholders about identified security weaknesses within an organization's infrastructure. This document outlines specific exploitable vulnerabilities, their potential impact, and the necessary remediation steps to mitigate risks. It serves as a critical communication tool for compliance and proactive defense, ensuring technical teams and management understand how to resolve flaws before they are exploited by attackers. Timely distribution of this letter is essential for maintaining robust data protection and organizational resilience against evolving digital threats.
Management Letter on Third-Party Vendor IT Security Controls
A Management Letter provides critical oversight regarding a third-party vendor's IT security controls. It typically accompanies a SOC 2 report, detailing specific control deficiencies, operational weaknesses, and recommended remediations identified during an audit. For organizations outsourcing data processing, reviewing this document is essential to assess residual risk and ensure the vendor maintains robust cybersecurity protocols. Understanding these findings allows management to implement necessary safeguards, ensuring compliance and protecting sensitive data from potential breaches within the supply chain.
What is a Management Letter on IT General Controls (ITGC) and Cybersecurity?
A Management Letter is a formal document issued by auditors that identifies internal control deficiencies, operational inefficiencies, and security vulnerabilities within an organization's IT infrastructure and cybersecurity framework. It provides actionable recommendations to mitigate risks related to data integrity, system availability, and unauthorized access.
Why are Information Technology General Controls (ITGC) critical for financial reporting?
ITGCs serve as the foundation of the IT environment by ensuring that application-level controls and data processing are reliable. Effective controls over program changes, access to programs and data, and computer operations are essential for auditors to place reliance on automated financial reports and prevent material misstatements.
What common cybersecurity weaknesses are typically highlighted in a Management Letter?
Common findings include weak password policies, lack of multi-factor authentication (MFA), inadequate patch management protocols, insufficient employee security awareness training, and poorly defined incident response plans. Addressing these weaknesses is vital for protecting sensitive corporate data and maintaining regulatory compliance.
How does a Management Letter differ from a formal Audit Opinion?
While an Audit Opinion focuses on the fairness of financial statements, a Management Letter is a value-add advisory document. It focuses on the "how" and "why" of operational risks, offering specific insights into strengthening the IT environment and cybersecurity posture beyond the minimum requirements of a standard financial audit.
What steps should management take after receiving an ITGC and Cybersecurity Management Letter?
Management should prioritize findings based on risk level, assign owners to each recommendation, and establish a timeline for remediation. Following up with a formal remediation plan demonstrates a commitment to strong corporate governance and helps ensure that previous control gaps do not escalate into significant deficiencies or material weaknesses in future periods.


Comments